All articles containing the tag [
Authentication
]-
Standardized Volkswagen German Server Keying And Security Audit Process For Enterprises
the standardized volkswagen german server key distribution and security audit process for enterprises introduces key management, access control, audit methods and compliance requirements to help enterprises establish auditable and secure operation and maintenance processes in the german environment.
German Server Server Key Distribution Key Management Security Audit Enterprise Security Standardized Process Compliance Data Sovereignty -
Deployment Tutorial Taiwan Cdn Cn2 Access Steps And Common Configuration Examples
detailed deployment tutorial: taiwan cdn cn2 access steps and common configuration examples, covering pre-preparation, network planning, dns/ssl, cache and return-to-origin settings, verification and monitoring, suitable for engineers and operations who want to optimize the access experience in taiwan.
Taiwan Cdn Cn2 Access Deployment Tutorial Cdn Configuration Example Taiwan Acceleration Cn2 Routing Dns Configuration Cache Strategy -
Vps Image Template And Automated Deployment Suggestions For Developers In Shatin, Hong Kong Computer Room
provide developers with vps image templates and automated deployment suggestions for the shatin computer room in hong kong, covering practical points such as image selection, security compliance, iac governance, ci/cd pipeline, network and monitoring optimization, etc., to facilitate improvement of deployment efficiency and stability.
Hong Kong Shatin Computer Room Vps Image Template Automated Deployment Developer Iacci/cd Operation And Maintenance Monitoring Network Optimization -
Best Practice Summary Of Vietnam 1gbps Vps Deployment Case From Live Broadcast To Large File Synchronization
this article summarizes the deployment cases and best practices of vietnam's 1gbps vps in live broadcast and large file synchronization scenarios, covering bandwidth planning, layered architecture, transmission strategy, security and operation and maintenance monitoring, to facilitate localized seo optimization and practical implementation.
Vietnam 1gbpsvps Vps Deployment Live Broadcast Deployment Large File Synchronization Bandwidth Planning Network Optimization Operation And Maintenance Monitoring Localized Deployment -
Hybrid Cloud Deployment Case: Hong Kong Server Is Easy To Use And The Local Computer Room Works Together
this article introduces hybrid cloud deployment cases, focusing on useful collaboration solutions for hong kong servers, covering architecture design, network interconnection, data synchronization, security compliance and operation and maintenance automation, and providing executable suggestions.
Hybrid Cloud Deployment Hong Kong Server Local Computer Room Collaborative Work Network Interconnection Data Synchronization Operation And Maintenance Automation Compliance -
Security Hardening Process: How Malaysia Optimizes Server Protection Against Ddos And Intrusion Detection
introduce the security hardening process in the malaysian environment, focus on server protection, ddos mitigation and intrusion detection deployment, and provide executable optimization suggestions and localized compliance considerations.
Security Hardening Malaysia Server Protection Ddos Protection Intrusion Detection Security Hardening Process Network Security Risk Assessment -
Account And Region Restrictions Analysis Of Possible Permission Reasons Why The Cf Vietnam Server Cannot Be Accessed
analyze common permission and region restrictions reasons why cf vietnam server cannot be accessed, covering account region locking, ip geographical detection, anti-cheating and risk control, client region mismatch, network and port troubleshooting and solution suggestions.
Cf Vietnam Server Unable To Enter The Server Regional Restrictions Account Permissions Regional Server Problems Game Connection Failure Vietnam Server -
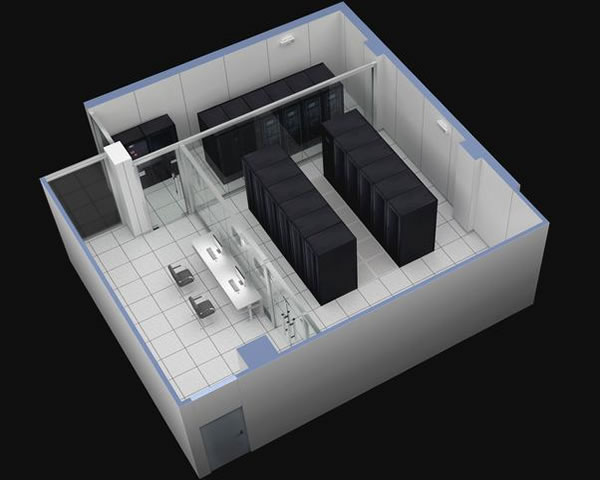
How To Implement Cross-computer Room Disaster Recovery And Data Backup Strategies In Taiwan Computer Room Server Cloud Space
this article provides systematic guidance on implementing cross-computer room disaster recovery and data backup strategies in taiwan's computer rooms and cloud space environments, covering practical suggestions such as risk assessment, backup types, replication technology, automation and security.
Taiwan Computer Room Cross-computer Room Disaster Recovery Data Backup Cloud Space Backup Strategy Off-site Disaster Recovery Rto Rpo -
Multi-region Expansion What Are The Hybrid Cloud And Multi-az Deployment Practical Guide For Singapore Servers?
a practical guide for technical decision-makers, it introduces the reasons for expanding singapore servers in multiple regions, hybrid cloud and multi-az deployment strategies, data consistency, traffic management, disaster recovery and security and other key points, including best practice suggestions that can be implemented.
Singapore Servers Multi-region Expansion Hybrid Cloud Multi-availability Zones Deployment Practices Disaster Recovery Latency Optimization Data Synchronization Load Balancing